Best One Hitters
Discreet Smoking Pipes for Convenient Relaxation
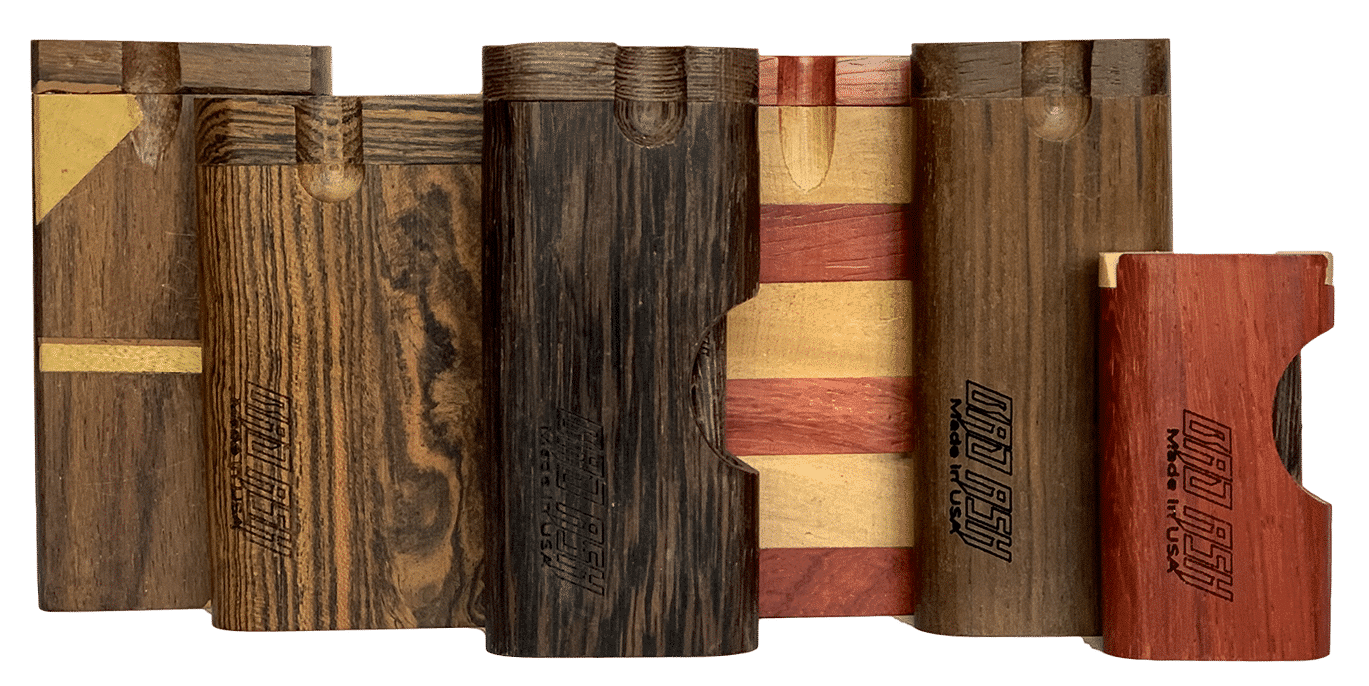
Wood One Hitter Dugouts & Pocket Pipes
Explore our one hitter amazon of the best dugout one hitters, wood chillums, metal incognito pipes, and smoking accessories. Best One Hitters aims to revive simple classics like the hitter box by partnering with local manufacturers.
Browse quality wooden dugouts, dugout pipe replacements, chillums, and pocket pipes.
Best One Hitters
Discreet Smoking Pipes for Convenient Relaxation
Wood One Hitter Dugouts & Pocket Pipes
Explore our one hitter amazon of the best dugout one hitters, wood chillums, metal incognito pipes, and smoking accessories. Currently, we are offering free shipping on our entire one hitter box inventory!
Browse quality wooden dugouts, dugout pipes replacements, wood chillums, and incognito pocket pipes.
High-Quality Wooden Dugouts
Choose from our large assortment of handmade wooden dugouts.
Wood and Glass Chillums
Twist Dugouts

Slide Dugouts

Double Dugouts

One Hitter Bats

Hand Pipes
Chillums

“The site was very user friendly and seamless check out made it all worth while. And when actually got the item! Game changer! Im super stoked with how awesome it is and the quality is Amazing! Im definitely a forever customer now.”
Misty P.
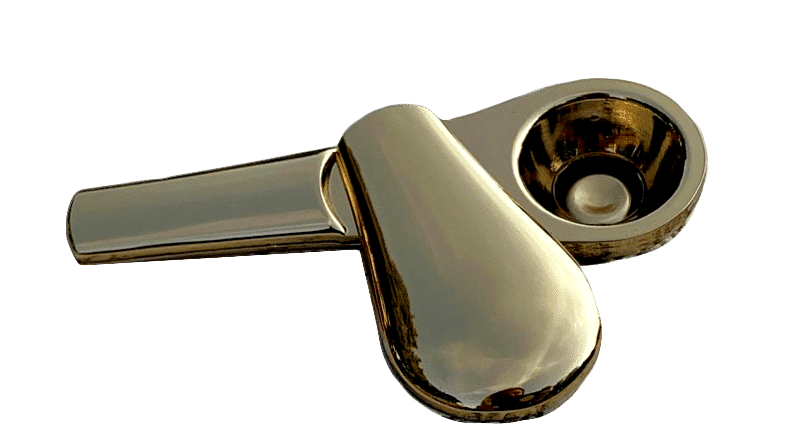
One Hitter Bats
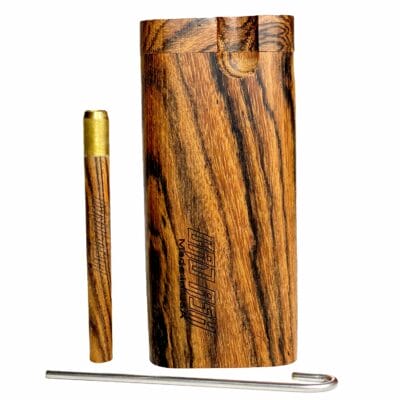
Choose either brass-tipped wood or surgery-grade titanium for your one hitter bats.
Browse One Hitter Dugouts
and Incognito Smoking Accessories

Best Dugout One-Hitters
Handcrafted by the Best Wooden Dugout Artisans
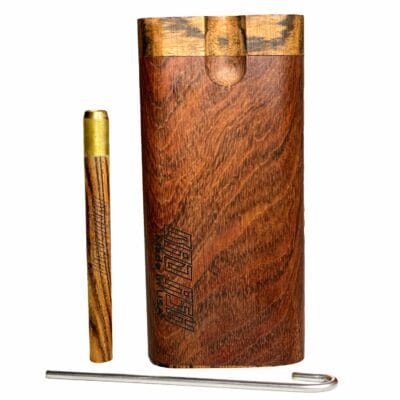
These fine pieces of craftsmanship blend talent and beautiful materials to create the best dugout one hitters.
These wooden hitter boxes are equipped with a digger bat for easy tobacco retrieval.
Quality Hitter Boxes
One hitter boxes are designed to discreetly smoke where you want, when you want. Before shipping, our hitter boxes undergo quality inspection to ensure you are getting the best dugout box possible.
While we didn’t invent the one hitter dugout, we elevated quality to offer you the best dugout system.
New wood one hitter boxes just added!
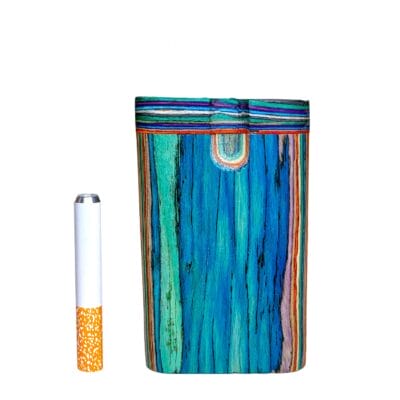
Unique Wood Dugouts
Forged from real wood, each dugout will be truly one-of-a-kind because of the wood grain patterns. Recently, we partnered with an Indiana family business to offer you the highest quality wooden dugouts available.
Drilled with precision and sanded by hand, you can expect a perfectly, unique wood dugout delivered to your door.
Cool Dugouts, Free Shipping
To celebrate 2021, Best One Hitters offers free shipping on all dugouts, chillums, pocket pipes, and bats also ship free. That’s right, we’ll ship you these cool dugouts for free in a discreetly labeled package.
Lucky Customers will Receive a Free Sticker!
Enhance your dugout by adding a cool aesthetic sticker from our friends at Cute Stickers World! Some lucky customers will receive a Best One Hitters sticker.
Dugout One Hitters on Sale
Limited Availability!
We are always improving and updating our hitter box designs based on customer feedback. That means new designs are always coming at ya! Subscribe to our mailing list for exclusive one hitter deals and new product updates.
Get these sleek dugout designs at a price that can’t be beat before they are gone! (Limited availability)
Sign Up for 10% Off
Sign up for our emails to get notified of new dugout designs and receive special offers! Plus get 10% off your first order.
Easy-Grip Digger Bat
Check the description of your dugout to see if it includes our spiked top digger bat which will allow you to grasp the perfect amount of tobacco in a single dip into your hitter box.
No more endless digging and twisting to fill your bat! If you understand the struggle, then you will enjoy this feature.
Not seeing what you want? Check out our friends over at The Silver Stick. They have some cool products, too.